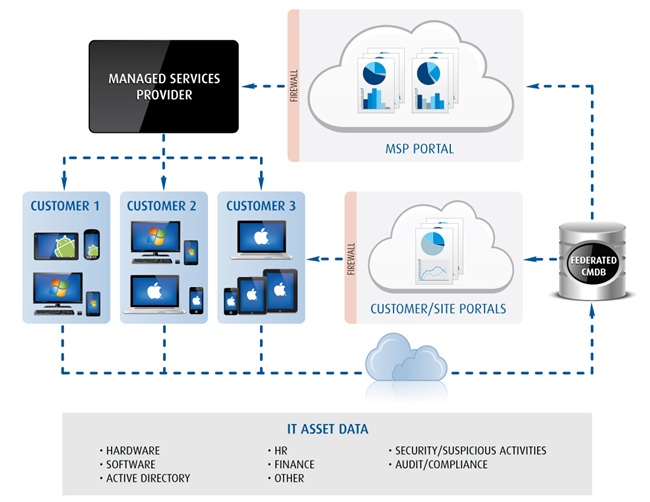
Absolute Software is pleased to launch our latest tool for IT administrators, Absolute Insight, a comprehensive web-based endpoint monitoring, security management solution for managed service providers (MSPs). With Absolute Insight, MSPs have a 360 degree view of each IT asset in all customer deployments, including relationships and dependencies within the organization based on information from hardware, software, active directory, HR, procurement, and other data sources. Using a cloud-based console,...
READ MORE