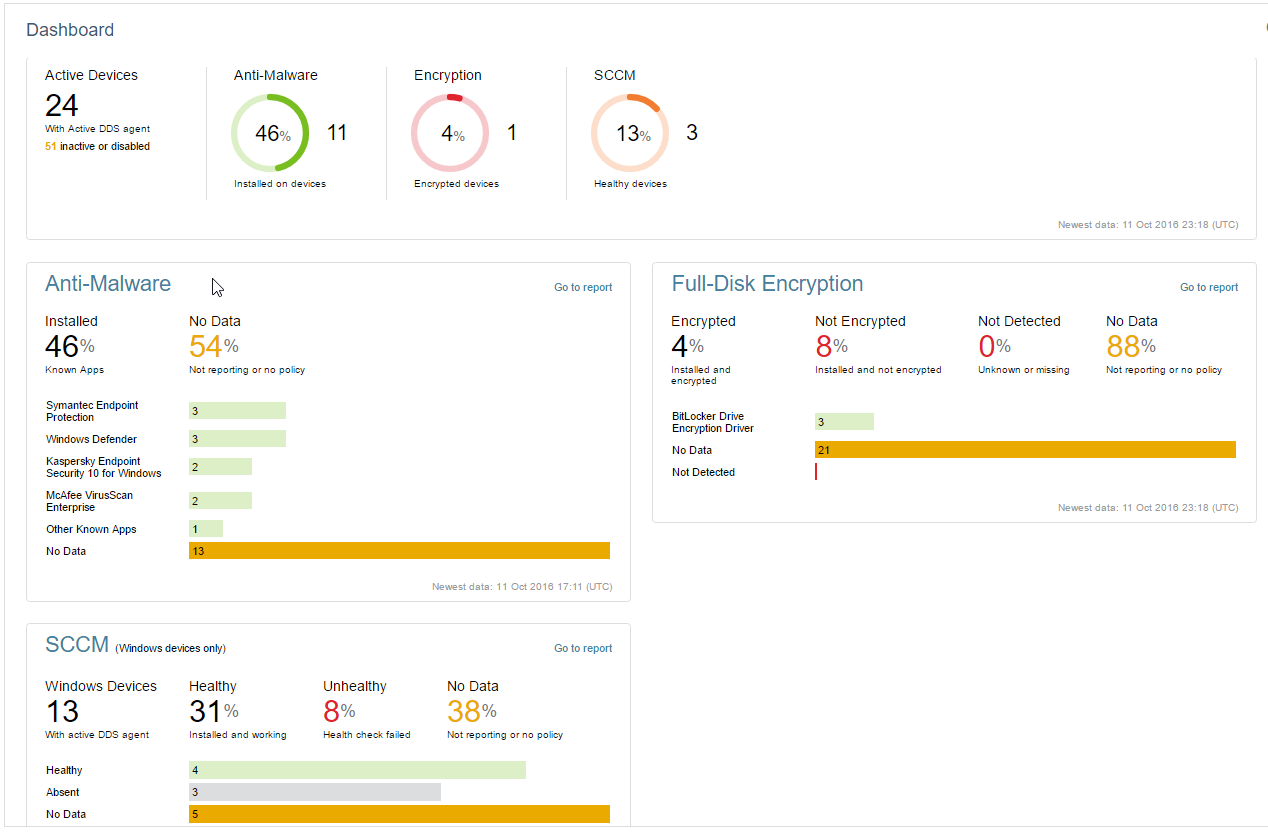
As part of the November 2016 release of Absolute Data & Device Security (DDS), we released new Security Posture Reports and a convenient Security Dashboard. With instant access to the health status of critical security layers and aggregate assessments of your entire security stack, you can take firm control of your security posture. Absolute DDS Provides Visibility into Multi-Layered Security In today’s constantly evolving cybersecurity landscape, no one security layer alone is sufficient...
READ MORE